Communication of Logmanager
The IP address 240.80.1.1 is used for some of the internal local IP communication between processes inside Logmanager. It can appear in logs which are created in the Logmanager itself.
Logmanager, for its proper operation, requires a range of allowed network ports. For the correct settings of firewalls, and other network elements, please use the following chart:
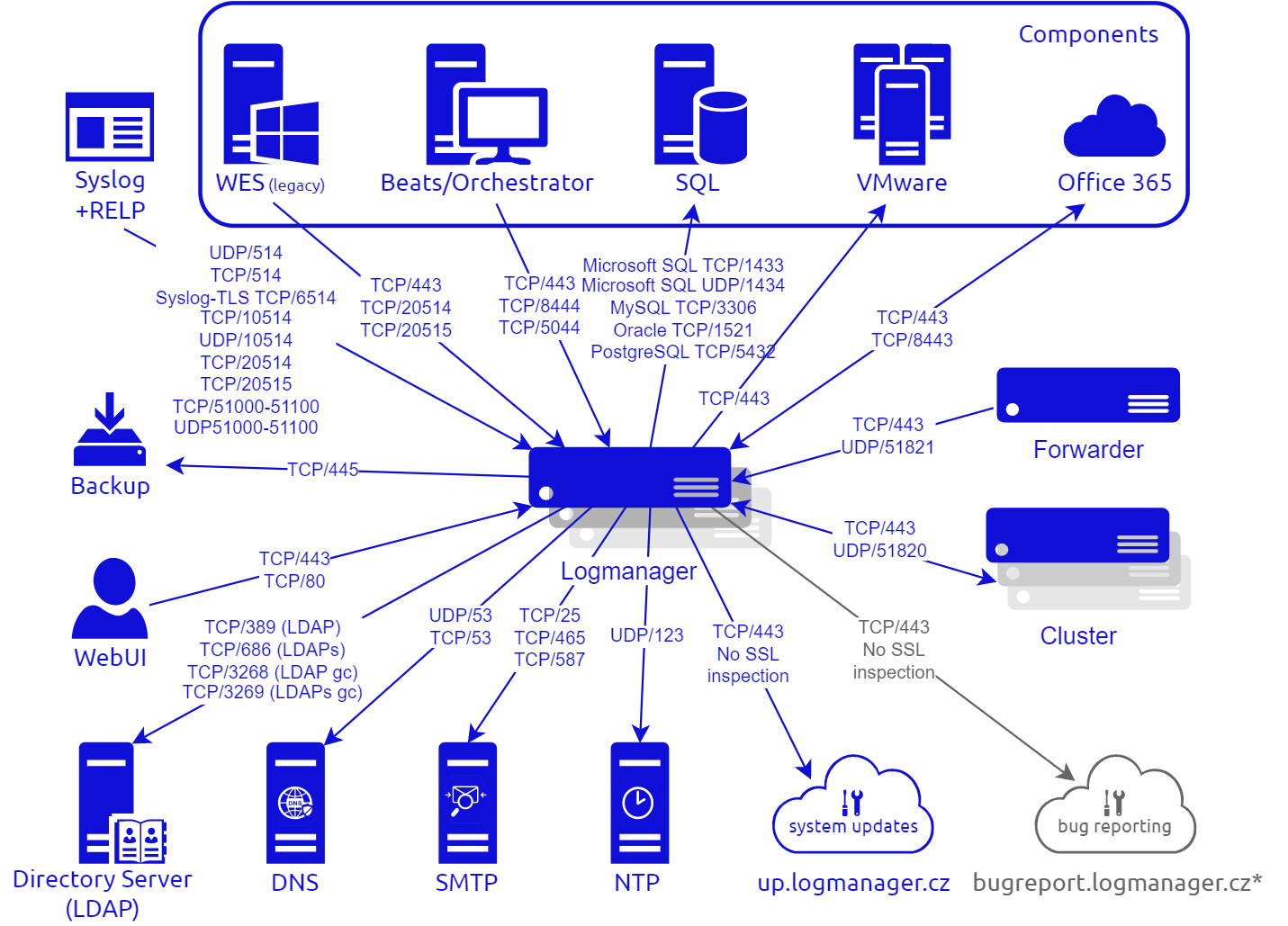
Communication diagram of Logmanager
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| Logmanager | DNS | 53 / UDP | |
| Logmanager | DNS | 53 / TCP | |
| Logmanager | LDAP | 389 / TCP | LDAP (users authentication) |
| Logmanager | LDAP | 686 / TCP | LDAPs (users authentication) |
| Logmanager | LDAP | 3268 / TCP | LDAP (AD Global Catalog) (users auth.) |
| Logmanager | LDAP | 3269 / TCP | LDAPs (AD Global Catalog) (users auth.). |
| Logmanager | NTP | 123 / UDP | Time synchronization |
| Logmanager | SMTP | 25 / TCP | Sending alerts, reports etc. |
| Logmanager | SMTP | 465 / TCP | SMTP authorization |
| Logmanager | SMTP | 587 / TCP | SMTP authorization |
| Logmanager | System updates | 443 / TCP | Requires access to: https://up.logmanager.cz/ (see Warning) |
| Logmanager | Bug reporting (see Note) | 443 / TCP | Requires access to: https://bugreport.logmanager.cz/ |
| Logmanager | O365 reading events from cloud | 443 / TCP | Access to entire internet or token renewal (without SSL inspection) |
Bug reporting - this communication is disabled by default, the operator must enable it for it to work. For more information see here: Automatically send error reports to vendor.
Access to the Logmanager up.logmanager.cz update server and Microsoft servers for reading events from the cloud requires transparent communication, i.e. without HTTPS/SSL inspection. Check your firewall settings to see if you are blocking communication or if you have HTTPS/SSL inspection (also known as MITM, or Man in the middle) enabled. If your firewall allows it, create a special unique rule for Logmanager to allow only the traffic you want.
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| RELP | Logmanager | 20514 / TCP | |
| Windows agent | Logmanager | 5044 / TCP | Windows agent input plugin |
| Syslog | Logmanager | 514 / UDP | |
| Syslog | Logmanager | 514 / TCP | |
| O365 log receive | Logmanager | 8443 / TCP | Receive events from O365 (without SSL inspection) |
| Syslog | Logmanager | 10514 / UDP | |
| Syslog | Logmanager | 10514 / TCP | |
| Syslog | Logmanager | 51000 - 51100 / UDP | |
| Syslog | Logmanager | 51000 - 51100 / TCP | |
| Syslog | Logmanager | 6514 / TCP | TLS |
Logmanager will automatically trunk all incoming Beats file messages that exceed size limit of 64 000 bytes. Every truncated message will be automatically marked as truncated. You can find more information here - Beats.
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| SSH | Logmanager | 22 / TCP |
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| Web | Logmanager | 443 / TCP | WebUI |
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| Logmanager | VMware | 443 (default) / TCP | HTTPS access |
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| Logmanager | Microsoft SQL | 1433 / TCP | SQL component |
| Logmanager | Microsoft SQL Server Browser | 1434 / UDP | SQL component |
| Logmanager | MySQL | 3306 / TCP | SQL component |
| Logmanager | Oracle Database | 1521 / TCP | SQL component |
| Logmanager | PostgreSQL | 5432 / TCP | SQL component |
| Source | Destination | Port / Protocol | Description |
|---|---|---|---|
| Logmanager Windows agent | Logmanager | 443 / TCP | Agent configuration |
| Logmanager Windows agent | Logmanager | 5044 / TCP | Windows agent input plugin |